How’s it going people? Everyone wants 100% secure applications but the problem is do 100% applications exist in the world? Answer is ‘Nope’. That’s bad but you can secure your application up to a certain extend by applying security. Hope you have read my last two articles on PHP Security. Article 1 & Article 2 where you can apply security at the application level. it’s time for you to read them before proceeding.
Today we are going to look at how to secure your Apache web server by adding security to it. Once you apply these configuration in your Apache web server you will be able to live safely. Let’s make the world a better place.
Note : Once make changes to your Apache configuration file(/etc/apache/apache2.conf) you should restart Apache web server using below command.
service apache2 restart
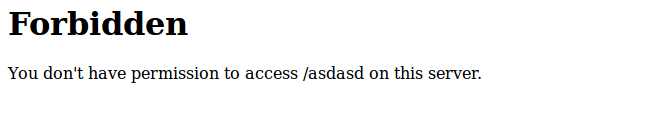
1. How to hide Apache version and OS
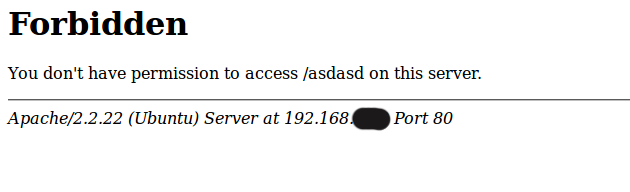
Open apache2.conf configuration file with vim editor and search for ServerSignature which is On by default. Set it to Off ,it tells Apache to stop showing the Apache version. Then set ServerTokens Prod which tells Apache to suppress the OS version info.
vim /etc/apache/apache2.conf
Set below two configurations.
ServerSignature Off ServerTokens Prod
2. Keep up to date
The Apache HTTP Server has a good record for security and a developer community highly concerned about security issues. But it is inevitable that some problems — small or large — will be discovered in software after it is released. For this reason, it is crucial to keep aware of updates to the software. – Apache Docs
3. Disable directory listing
When index.php/index.html is not present in a directory by default Apache list all the content of the particular document directory. Turn off directory listing by using Options directive in apache2.conf file as shown below.
<Directory /var/www/html>
Options -Indexes
</Directory>
4. mod_security and mod_evasive modules
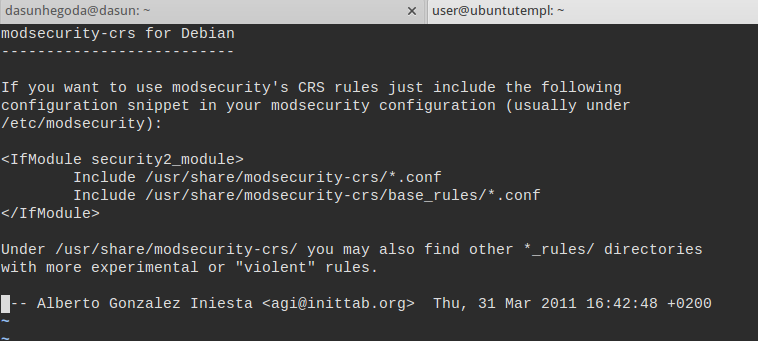
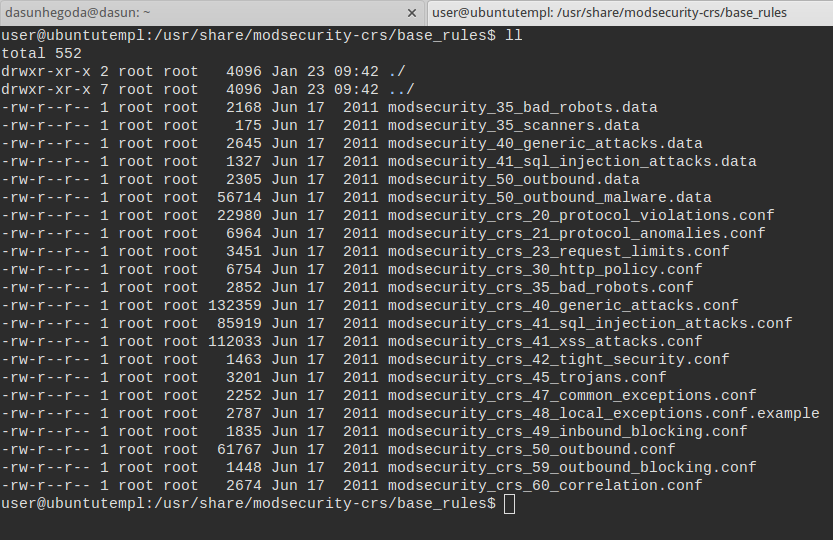
mod_security
Mod_security is an apache module which helps to be protected from various attacks. Let’s install mod_security.
apt-get install libapache2-modsecurity a2enmod mod-security /etc/init.d/apache2 restart
Verify if the mod_security module was loaded.
apachectl -M | grep --color security
Then you have to do some configurations as mentioned in the link. Read more on mod_security.
mod_evasive
mod_evasive is an Apache to provide evasive action in the event of an HTTP DoS or DDoS attack or brute force attack. Let’s install mod_evasive.
apt-get install apache2-utils apt-get install libapache2-mod-evasive a2enmod mod-evasive /etc/init.d/apache2 restart
Let’s create a log file folder for mod_evasive
mkdir /var/log/mod_evasive chown www-data:www-data /var/log/mod_evasive/
Add the below configurations to the /etc/apache2/mods-available/mod-evasive.conf file.
<ifmodule mod_evasive20.c> DOSHashTableSize 3097 DOSPageCount 2 DOSSiteCount 50 DOSPageInterval 1 DOSSiteInterval 1 DOSBlockingPeriod 10 DOSLogDir /var/log/mod_evasive DOSEmailNotify email@yourdomain.com DOSWhitelist 127.0.0.1 </ifmodule>
Read more here on mod_evasive.
5. Disable unnecessary modules
Below is the list of modules that are enabled by default but often not needed. To disable the particular module, you can insert a “#” at the beginning of that line. Read more here and here.
auth_basic_module modules/mod_auth_basic.so auth_digest_module modules/mod_auth_digest.so authn_file_module modules/mod_authn_file.so authn_alias_module modules/mod_authn_alias.so authn_anon_module modules/mod_authn_anon.so authn_dbm_module modules/mod_authn_dbm.so authn_default_module modules/mod_authn_default.so authz_host_module modules/mod_authz_host.so authz_user_module modules/mod_authz_user.so authz_owner_module modules/mod_authz_owner.so authz_groupfile_module modules/mod_authz_groupfile.so authz_dbm_module modules/mod_authz_dbm.so authz_default_module modules/mod_authz_default.so ldap_module modules/mod_ldap.so authnz_ldap_module modules/mod_authnz_ldap.so include_module modules/mod_include.so log_config_module modules/mod_log_config.so logio_module modules/mod_logio.so env_module modules/mod_env.so ext_filter_module modules/mod_ext_filter.so
6. Apache with SSL
The Apache HTTP Server module mod_ssl provides an interface to the OpenSSL library, which provides Strong Encryption using the Secure Sockets Layer and Transport Layer Security protocols. – Apache SSL
There are plenty of article written on this topic, so I’m not going to rewrite. Refer this article to get SSL on Apache.
7. Apache logging
Apache logging provides more information on what’s happening in the server.
In order to effectively manage a web server, it is necessary to get feedback about the activity and performance of the server as well as any problems that may be occurring. The Apache HTTP Server provides very comprehensive and flexible logging capabilities. – Apache Logs
See the below image about Apache log levels.
Okay now let’s configure logs in your virtual hosts. If you don’t know much about virtual host time to read this article.
<VirtualHost *:80> DocumentRoot /var/www/html/dasunhegoda.com/ ServerName www.dasunhegoda.com DirectoryIndex index.htm index.html index.php ServerAlias dasunhegoda.com ErrorDocument 404 /404.php LogLevel warn ErrorLog /var/log/apache/dasunhegoda.com_error_log CustomLog /var/log/apache/dasunhegoda.com_access_log combined </VirtualHost>
These are most used configurations to secure an Apache web server. If you have any questions let me know in the comments below. Your feedback is highly appreciated(happy-face).
![]()



You found to be so strict in security. Even you blurred your private IP address :) nevertheless Good work buddy (y)
Thanks